Quantum-Safe Cryptography Is No Longer a Future Problem — It's a 2026 Procurement Decision
SandboxAQ's integration of large quantitative models into Google Cloud marks a turning point: post-quantum cryptography has moved from academic theory to enterprise procurement. With NIST standards finalized and regulatory mandates tightening, financial services and defense organizations must act now or risk being caught exposed.
For years, quantum-safe cryptography lived comfortably in the future tense — something enterprises would "eventually" need to address. That comfortable distance just collapsed. SandboxAQ's integration of large quantitative models (LQMs) into Google Cloud, combined with NIST's finalization of post-quantum cryptography (PQC) standards in August 2024 and the selection of HQC as an additional algorithm in March 2025, means the post-quantum transition has officially entered procurement territory. If your organization hasn't started mapping its cryptographic infrastructure, you're already behind schedule.
From Standards to Spending: The Enterprise Reality of PQC Migration
The regulatory signal is clear and getting louder. The U.S. OMB M-23-02 memorandum requires federal agencies — and by extension their supply chains — to appoint migration leads, inventory quantum-vulnerable cryptography, and prioritize high-impact systems for remediation. Meanwhile, the U.K.'s incoming Cyber Security and Resilience Bill is set to extend similar obligations to critical infrastructure suppliers. For financial services and defense contractors, compliance is no longer optional — it's a contracting requirement in the making.
And the price tag is real. According to enterprise migration guides, organizations should budget for a layered stack of new capabilities:
- Cryptographic discovery platforms: $200,000–$500,000 annually to map where vulnerable algorithms live across the estate
- Dedicated PQC migration teams: 3–5 FTEs running $500,000–$1.5M per year
- HSM replacement programs: $200,000–$2M depending on fleet size — vendors like Thales have already updated their Luna HSM line to support PQC algorithms
- Custom application remediation: $500,000–$3M depending on portfolio complexity
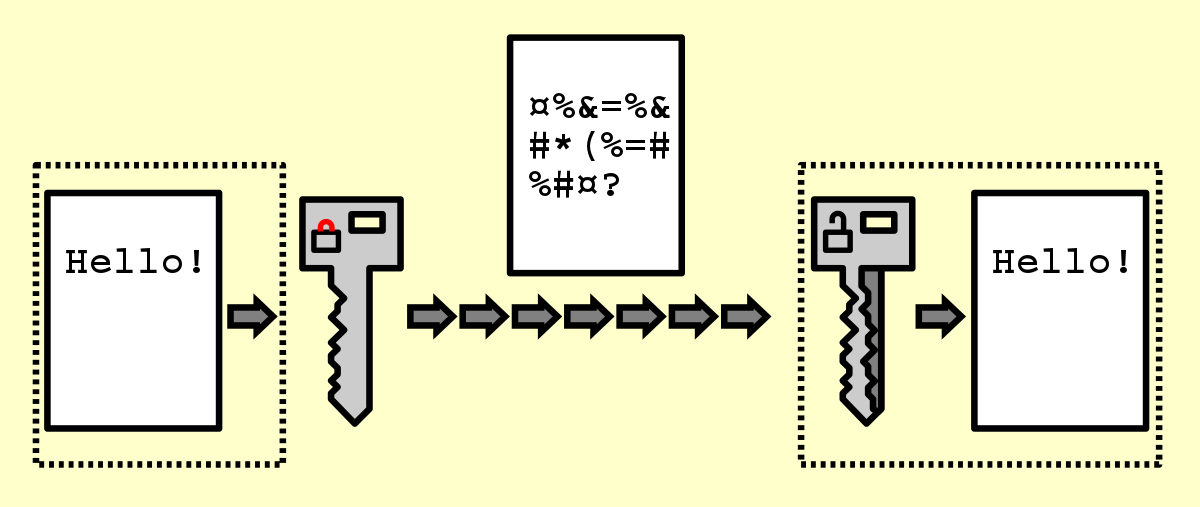
That's a multi-million dollar program. But it's also a finite, manageable one — especially if organizations adopt a hybrid transition model, where classical and quantum-safe algorithms run in parallel. This approach maintains backwards compatibility during what analysts expect to be a 5–10 year transition period before classical algorithms can be safely retired.
Crypto-Agility Is the Real Strategic Goal — Not Just Algorithm Swaps
Here's where many organizations get the framing wrong. The goal isn't to rip out RSA and replace it with ML-KEM everywhere by a fixed deadline. The goal, as security strategists are increasingly emphasizing, is crypto-agility — building systems where migrating from today's quantum-safe algorithms to tomorrow's is a configuration change, not a ground-up rebuild. Given that NIST added HQC (a code-based algorithm) to its PQC toolkit just this year for mathematical diversity, the standards themselves are still evolving. Locking into any single approach without agility baked in is a strategic mistake.
The vendor landscape reflects this maturity. Companies like QuSecure offer quantum-safe orchestration platforms, while Quantum Xchange provides a hybrid migration path — start with software-based PQC, add hardware Quantum Key Distribution (QKD) later as budgets and infrastructure allow. IBM is leaning into lattice-based algorithm expertise built during the NIST standardization process itself, offering quantum-safe transformation services at enterprise scale. SandboxAQ, meanwhile, is embedding LQMs directly into cloud infrastructure — using machine learning to accelerate cryptographic analysis, vulnerability detection, and migration planning at a pace no manual audit team can match.
For key management specifically, quantum random number generation (QRNG) is emerging as a critical component. Classical pseudo-random number generators introduce subtle but exploitable weaknesses in key creation — QRNG eliminates that attack surface entirely, and cloud-integrated QRNG services are now commercially available.
The "Harvest Now, Decrypt Later" Clock Is Already Ticking
There's a reason urgency is climbing even though cryptographically relevant quantum computers aren't here yet: "harvest now, decrypt later" attacks are already underway. Sophisticated state-level adversaries are intercepting and storing encrypted government, financial, and defense communications today, betting they'll be able to decrypt them once quantum hardware matures. Any data with a sensitivity lifespan longer than five to ten years — classified intelligence, long-dated financial instruments, patient health records, intellectual property — is effectively already at risk.
That changes the calculus entirely. Organizations in financial services and defense can't wait until quantum computers are demonstrated in the wild. By then, the data is already gone. The migration timeline isn't driven by when the threat arrives — it's driven by how long your data needs to stay secret.
The post-quantum era isn't approaching — it's being priced into enterprise budgets right now. With NIST standards finalized, cloud platforms embedding quantum-safe tooling, and regulatory mandates hardening across the U.S. and U.K., 2026 is the year crypto-agility roadmaps move from the CISO's whiteboard to the CFO's approval queue. Organizations that treat this as a future problem will find themselves scrambling to meet compliance timelines with legacy infrastructure and an eye-watering remediation bill. The ones who start the inventory, stand up the hybrid architecture, and partner with vendors building for this transition will be the ones writing the case studies — not reading them in a panic.